If you're reading this you're probably aware that at 5 am this
morning first direct's Twitter account
was hijacked and used to spam our followers. We'd like to apologise for
the message itself (no need to repeat it) and for the way we dealt with
it in the first instance.
We would like to offer you some explanation for our actions...
How did it happen?
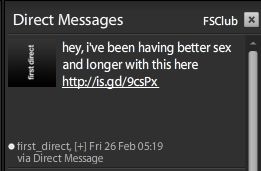
This morning (about 00.30 am) we received a rather salacious Tweet
from one of our followers (their account had been hijacked too) and
whilst checking it out proceeded to read the other direct messages we'd
received. One direct message was from a trusted source it read "ha ha
is this you?" and included a link which we unthinkingly clicked on.
We
can confirm that our Twitter password is extremely secure (a long
string of randomised characters, and regularly changed), and the only
reason they were able to gain access to our account was through the
mistake we made. Obviously we changed our password as soon as we
realised what had happened (and we have revoked the OAuth access of the
spam generator), so our account is secure again.
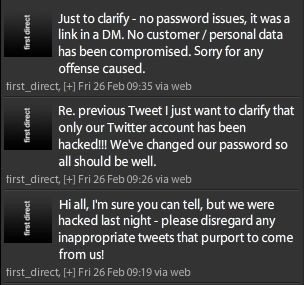
Why did we respond the way we did?
We tweeted quickly out of a desire to re-assure people and perhaps
should have gone straight to the third of our three tweets. We should
have got an apology up sooner, and we probably shouldn't have used the
word "hack". Twice.
We've now put steps in place to make sure it
doesn't happen again.
Have any other first direct accounts been
tampered with?
Absolutely not. This was an isolated incident affecting our Twitter
account only.
Final word
This is new to us and to the financial services sector as a whole. We
made a mistake, fixed it as soon as possible and we're taking steps to
ensure it doesn't happen again. We're very sorry, but we are only human
afterall.