It fascinates me when we talk about ‘identity’ that we always seem to think of identity management as being a single thing ... but it’s not.
First, there’s the use of identity for identification; second for authentication; third, for verification; and fourth for fulfilment.
Then there are the many instances of providing and proving identification: at a bank, at an airport or border control, at a vehicle hire firm or other high cost rental, when opening a telephone account or similar service, when picking up tickets for a concert, etc.
Finally, there are the many reasons for needing identity checks, from tracking money laundering and politically exposed persons (PEPs) to fraud and identity theft issues to just checking that you are who you say you are.
Although these all sound the same, they have distinct differences and is the reason why there are so many identity solutions out there. Generally, such solutions fall into a catchment of being for an anti-fraud focus or for a verification process, with the process being based upon:
- Something you know, such as a PIN, Password or Personal Fact
- Something you have, such as Card, Token or Telephone
- Something you are, such as a Fingerprint, Voice or other Biometric
- Somewhere you are, based upon GPS location or similar proximity analysis
- Some way you behave, such as your general activities, channel usage and location
Obviously the five areas above are also inter-connected, as you could use a PIN, Biometric and Telephone along with location services to verify a user based upon five-factor authentication rather than two. But we don’t do that today, and some banks struggle with even one factor authentication.
You cannot be serious I hear you cry, but no, it’s true.
Ring your bank and pretend to be someone else.
I’ve done it.
I had to pretend to be my father-in-law and it was easy once you got the bravado together to claim to be someone you’re not.
So the question of identity for authentication and verification is still not good enough.
What are the potential solutions out there?
Generally, further variations on the above.
For example, I recently went to a presentation by a number of firms that use the words identity in their company name. Both firms were focused upon improving password security by offering easier password access and control.
I then got a call from another firm with identity in their name, and they wanted to talk to me about biometrics.
A third firm offered to provide mobile-based authentication services.
So let’s look at these variations in a little more depth.
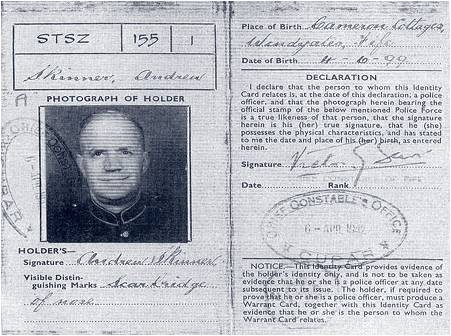
First, the something we have.
This is the most basic form of identification – a document, validated by an authority, that says: “yes, it’s you”.
Often a card and sometimes a card with your photograph on it, this identification has been around since the war.
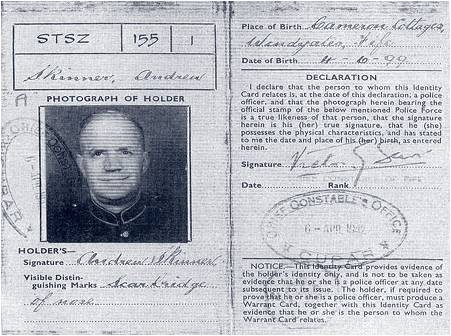
The trouble with this form of identity is that it can be forged, copied, stolen and easily used by another card holder.
Therefore, we introduced the something you know.
The idea here is that there is a secret code that goes with the card to show that not only is the person presenting the card the owner, but they can prove it.
The most common something you know is a Personal Identification Code, or PIN.
PINs are generally allocated by the bank but can be changed to whatever you want.
Although secure therefore, it’s easy to second guess or, due to Chip & PIN, shoulder-surf and steal.
Equally, PINs can be hacked and compromised via intelligent machine-in-the-middle attacks and so banks introduced a four-digit PIN password enhancement by asking things like date of birth and mother’s maiden name.
It soon became obvious that criminals could find out such information from public record and so we are now in a world of much more complex codes and secrets.
For example, GrIDsure offer a pattern-based PIN so that criminals cannot predict your PIN numbers. Equally, RSA security offer lots of tokens and keys to generate one-time passwords on top of basic identity information, to ensure that a criminal is foiled.
Unfortunately, in the latter case, many of these efforts just add to the effort required for the customer every time they are trying to make a payment or access the bank service. For example, we have the Chip Authentication Program (CAP) and Personal Card Readers (PCR) in the UK for online payments processing.
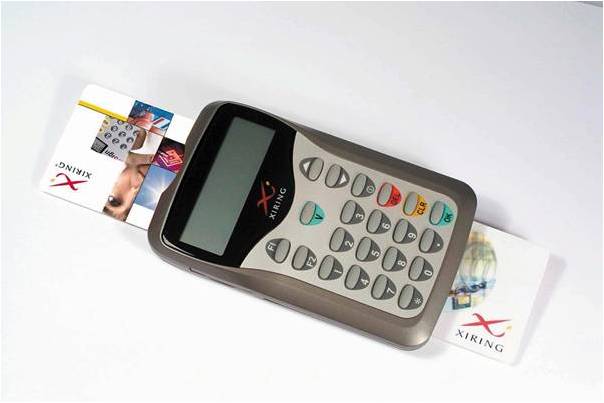
The trouble is that you have to have the terminals with you and, even if you do, people use them so infrequently that they often forget the process. As a result, their use of online payments falls whilst PayPal goes from strength to strength.
The reason?
PayPal is simple, easy and convenient, but PCRs are not.
Equally, what is really interesting in the two instances above, is that these things are already being side-tracked by the mobile telephone, which offers something you have that is unique – your SIM card and telephone number – along with an interactive dialogue for access to PINs and One-Time Passwords.
In addition, it offers an easy way to track where you are, and hence can be a good way of triangulating information for a bank. For example, if someone tries to withdraw cash or make a payment in New York when their mobile telephone GPS signal is being picked up in San Francisco, the bank could immediately question such transactions.
Therefore, I wholly expect the mobile telephone to become the key to most forms of identification.
The mobile can even play directly into the biometrics field, thanks to fingerprint recognition and even apps under discussion that will use the mobile telephone’s camera for iris or face recognition. In particular, the work of Voice Commerce to create voice biometric payments is of interest here.
Voice Commerce is now a PSD-approved Payments Institution and Visa Partner, all based upon mobile voice biometric services.
So where does that take us?
The mobile telephone becomes the unique identity management system for future financial services?
Sure, it provides a clear capability to track behaviour and location, along with easy verification and validation of something you have and something you know and potentially something you are.
But is that it?
What happens if you lost the telephone?
What happens if you forget the codes or passwords?
Is Voice Biometrics really ready for prime time?
What I am really asking is: what is the process on the other end of the telephone that’s required?
This still therefore mandates a clear bank identity management system, shared across multiple institutions, which can allow the user to access finance with just a single sign-on rather than multiple sign-ons.
That’s the thought for next generation financial services. A simple multibank, cross-border identity system that can work easily and simply and conveniently behind the mobile bank interface.
Hmmmm ... I wonder what system that could be?
Whichever system it is has to have a number of key features.
First, it will not just be a technology solution, as there must be clear and recognised policy, legal and operational rules which allow the shceme to operate across bordres and banks.
Second, an identity scheme cannot just be a “number”. Numbers are too easy to break, and you therefore must have a name specified and associated with the number in order for the identity management system to allow transactions to be truly non repudiable, as in legal.
Third, solutions have to be massively scalable, which means cloud-based today.
Fourth, it must be capable of supporting multiple applications across multiple geographies and multiple industry silo’s.
And, whilst achieving all of the above, it needs to be simple to use but unbreakable.
Now that’s not so difficult is it?
Chris M Skinner
Chris Skinner is best known as an independent commentator on the financial markets through his blog, TheFinanser.com, as author of the bestselling book Digital Bank, and Chair of the European networking forum the Financial Services Club. He has been voted one of the most influential people in banking by The Financial Brand (as well as one of the best blogs), a FinTech Titan (Next Bank), one of the Fintech Leaders you need to follow (City AM, Deluxe and Jax Finance), as well as one of the Top 40 most influential people in financial technology by the Wall Street Journal's Financial News. To learn more click here...