I went to see a screening of a new film about Anonymous last
night called We Are Legion: the Story of
the Hacktivists.
The film tells the story about the rise of Anonymous and the
hacktivism movement, portrayed through interviews with many of the key players.
The film includes some of my favourite discussion areas,
such as the fall of HBGary and Aaron Barr (who appears in the movie looking dreadful) and the rise of the Occupy Movement,
as well as some areas I haven’t covered in depth here, such as the CULT OF THE DEAD COW, the Long Cat and the Scientology versus 4Chan war. The latter wouldn’t sit on the Finanser blog
as they were not targeting financial markets, although they do serve to lay
down much of the chronology of where Anonymous and Occupy came from.
The film defends the movement as a pure online ‘sit-in’ that
poses no real threat to business or governments. It portrays the potential fines of the “PayPal14”
– the fourteen people who have been arrested for participating in the ‘sit-in’
against PayPal, Visa and MasterCard after they were aligned against Wikileaks –
as being extreme. A $250,000 fine with the threat of a 15 year jail sentence is the ultimate penalty these demonstrators
face, which is a harsher full sentence than a paedophile receives (maximum 12
years).
The director, Brian Knappenberger, and his interviewees believe
that online activism is no different to physical activism, and that a
demonstration on the street is just the same as a denial of service attack.
The film claims that anonymous and its equivalents pose little threat therefore - it is just peaceful demonstration - and that the threats of Duqu, Flame, Stuxnet and their equivalents are far worse.
If anything, the film has one slight weakness in that it does
not include any view on where this movement might move in the future. In fact, the director lets the players in the
anonymous movement tell their story with no judgements, apart from those made
in the edit suite.
Nevertheless, it has received multiple selections for the
world’s top documentary festivals

And, to make up for this shortfall, I will blog tomorrow
about where anonymous and hacktivism could go in the future.
Meanwhile, in the interests of completing the Uprising journey, let’s look at the history of
the hacktivism movement and where it sits today as portrayed through the eyes
of Mr. Knappenberger.
This is an edited and shortened version of the History of Hactivism from the We Are Legion Documentary website:
September 1946: The Tech Model Railroad Club
The
Tech Model Railroad Club is founded at the Massachusetts Institute of
Technology in 1946. The word “hack” was originally used at MIT to describe
elaborate college pranks. As used by the TMRC, the word was also understood to
mean a feat “imbued with innovation, style, and technical virtuosity.” (Steven
Levy, Hackers: Heroes of the Computer Revolution.)
October 1971: The “Phreaker”
Ron
Rosenbaum gains public attention with his article in Esquire called “Secrets of
the Little Blue Box” where he coins the term “phreaker” to describe
technologists manipulating the phone system.
November 1971: Jobs and Wozniak make a Blue Box
Steve
Jobs and Steve ‘Woz’ Wozniak build “blue boxes,” illegal electronic devices
used to generate the tones telephone networks once used to switch long distance
calls. The two sell the boxes to students eager to get free long distance, and
Wozniak reportedly once uses one to call the Vatican while posing as Secretary
of State Henry Kissinger.
September 12, 1981: Chaos Computer Club
Chaos
Computer Club forms in Berlin, Germany. Recognizing “currently emerging
electronic data networks,” the CCC wants to use them creatively with a belief
that governments should operate transparently and that information should be
free. The CCC has become one of the world’s biggest hacker organizations.
1984: CULT OF THE DEAD COW
CULT
OF THE DEAD COW (cDc) forms in Lubbock, Texas. The group had a stated goal of “Global
Domination Through Media Saturation” and would later, among other actions,
declare war on the Church of Scientology in 1995.
January 12, 1984: 2600
2600:
Magazine gets its start. The name refers to the phreaker discovery that the
transmission of a 2600 hertz tone over a long-distance connection gains access
to “operator mode” of the telephone system.
October 16, 1989: Political Computer Worm
WANK,
a computer worm allegedly created by two hackers in the U.S., attacks a
computer network shared by NASA and the US Department of Energy in protest of
US nuclear policies.
July 10, 1990: EFF Begins
The Electronic Frontier Foundation is formed. Consisting of lawyers,
policy analysts, activists, and technologists it calls itself the first line of
defense “when our freedoms in the networked world come under attack.”
November 5, 1994: The Zippies
An
electronic civil disobedience collective action called “The Intervasion of the
UK” was carried out by a group called the Zippies to protest a proposed law
that would outlaw outdoor music festivals. On Guy Fawkes Day, the group
launches a denial of service attack - in this case an “ebomb” - against the UK
government website, which succeeds at shutting it down for at least a week. The
action is regarded as the first time a denial of service attack was used as a
form of civil disobedience.
December 21, 1995: Net’Strike
The
Strano Network stages a one-hour Net’Strike to shut down various French
government websites in opposition to the country’s nuclear and social policies.
Strano Network’s Net’Strike is considered one of the earliest documented
hacktivist protests.
1996: Hacktivism
CULT
OF THE DEAD COW member Omega coins the term “hacktivism” - loosely defined as
the use of hacking as a form of political protest, subverting government
surveillance of repressive regimes and the ideal that access to information is
a basic human right.
1997: Electronic Disturbance Theater
The
Electronic Disturbance Theater forms in New York. Using the Mosaic browser the
group begins to experiment with Denial of Service as a form of “virtual sit-in.”
1998: The “Virtual Sit-In”
Electronic
Disturbance Theater conducts “virtual sit-ins” on the websites of the Pentagon
and the Mexican government bringing attention to the massacre of a group of
indigenous people by paramilitary forces in Chiapas, Mexico.
May 19, 1998: The L0pht says they can shut down the entire
internet in 30 minutes
Testifying
before congress using their hacker names, members of the L0pht “hackers think
tank” say they could shut down the internet in 30 minutes.
August 1998: Back Orifice Debuts
CULT
OF THE DEAD COW releases “Back Orifice,” a free download that allows users to
hack and control computers remotely using the Windows operating system.
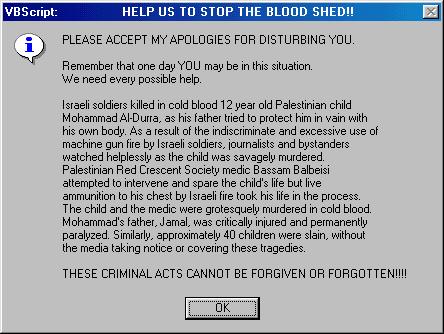
March 2001: The Injustice Virus
Pro-Palestinian
hackers release the “Injustice worm.” The virus steals email addresses from
Microsoft Outlook and uses them to send out a political message about the
killing of a Palestinian girl by Israeli soldiers.
June 20, 2001: Lufthansa Airlines Website Hit
German
activists organize a virtual sit-in on the website of Lufthansa Airlines, after
its planes are used to deport undocumented immigrants out of Germany.
September 20, 2002: Tor
The
online anonymity system Tor is released. Tor conceals a user’s location from
surveillance or analysis by directing internet traffic through a network of
servers.
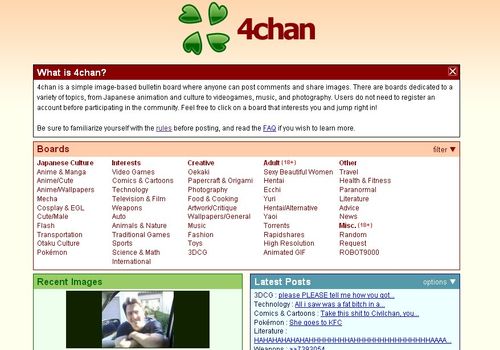
October 2003: 4chan Launched
Christopher
“moot” Poole launches 4chan. The site’s /b/ board is considered the birthplace
of Anonymous.
July 12, 2006: The Habbo Hotel Raid
/b/
users flock to Habbo Hotel using hundreds of avatars with large afros and gray
suits. They disrupt the game and - most infuriating to users - block the
entrance to the pool.
October 4, 2006: Wikileaks launched
Wikileaks,
the publisher of private or classified material from leaks, anonymous news
sources and whistleblowers begins operations.
December 2006: Hal Turner
Users
of /b/ DDoS the website of conservative shock jock and white nationalist Hal
Turner and publish his and his parents’ home phone numbers. Members of /b/ also
send pizzas, industrial materials and escorts from Craigslist to his house.
January 10, 2008: Hal Turner calls it quits
Hal
Turner says he is quitting his radio show and separating from the “pro-white”
movement after hackers claim to have uncovered emails suggesting that he was
working with the FBI. The FBI declined to comment on its involvement with Turner.
Turner is later jailed for inciting injury and threatening judges of the United
States Court of Appeals.
January 14, 2008: Tom Cruise Video
A
video interview with Tom Cruise produced by the Church of Scientology is leaked
on YouTube. Claiming copyright infringement, Scientology demands the video be
taken down.
January 21, 2008: Project Chanology
Anonymous
launches Project Chanology via a YouTube video titled “Message to Scientology.”
The group vows to “expel” the Church from the Internet, “and systematically
dismantle the Church of Scientology in its present form.”
January 26, 2008: Chanology Expands
Anonymous
releases a second video message on YouTube calling for worldwide protests
outside of Scientology centers on February 10, 2008.
February 10, 2008: Worldwide Scientology Protests
Approximately
7,000 people in 100 cities demonstrate in front of Church of Scientology
centers worldwide. Many don Guy Fawkes masks inspired by the graphic novel and
film “V for Vendetta” in order to conceal their identities.
April 18, 2009: Telecomix is founded
Telecomix
is founded on the day the FRA law, which allows the Swedish government to
warrantlessly wiretap all telephone and Internet traffic that crosses Sweden’s
borders, is passed by Parliament. The decentralized cluster of hacktivists is
committed to freedom of expression.
April 5, 2010: Collateral Murder Video
Wikileaks
releases the “Collateral Murder Video” which shows a U.S. Army Apache
helicopter in Baghdad in 2007 opening fire on a group of men. Among the dead
were two Reuters News employees.
July 25, 2010: Afghan War Diary
The
Afghan War Diary is released by Wikileaks.
November 28, 2010: Cablegate
Wikileaks
releases 251,287 classified diplomatic cables from the U.S. State Department.
The cables contain analysis from world leaders, and diplomats’ assessment of
host countries and their officials. To date, this is the world’s largest
release of classified material.
December 3, 2010: PayPal Blog Hit
Anonymous
send out a Distributed Denial of Service (DDoSes) attack on PayPal’s blog,
after the online payment giant says it ceased processing donations made to
WikiLeaks.
December 8, 2010: Operation Payback Targets Paypal and Major
Credit Card Companies
Paypal.com,
MasterCard.com and Visa.com are taken offline temporarily for cutting off
funding services for WikiLeaks.
January 2, 2011: Anonymous Targets Tunisa
Anonymous
launches a DDoS attack on Tunisian government websites in support of Arab
Spring protestors.
January 5, 2011: Thank you, Anonymous
Tunisians
living in Germany thank Anonymous for taking down various Tunisian government
websites.
January 20, 2011: Care Packages for Egyptian Protestors
Telecomix
& Anonymous reach out to aide Egyptian Protesters. A 160-page manual on how
to circumvent online censorship and a “care package” that contains instructions
on how to deal with tear gas is translated into Arabic and sent to Arab Spring
demonstrators.
January 27, 2011: Operation Payback Arrests
Five men are arrested in England in connection with Operation Payback. Following the arrests in England, the FBI
obtains more than 40 search warrants and raids the homes of suspected
participants involved in Operation Payback, in the U.S.
February 2, 2011: Egyptian Government Website Shut Down
In
support of the Arab Spring protests, Anonymous shuts down Egypt’s official
government website.
February 5, 2011: HBGary
HBGary
Federal, a computer security firm is hacked after CEO, Aaron Barr claims he has
unmasked the identities of the core members of Anonymous. On February 7, 2011,
over 40,000 internal emails are leaked as a result of the breach.
March 14, 2011: Bank of America
Anonymous
leaks a series of email correspondence between employees at Balboa Insurance, a
bank owned by Bank of America until 2011, to expose corrupt lending practices.
The emails center on requests to delete reference numbers from specific loan
documents in order to make them untraceable.
April 2011: The Birth of LulzSec
Two
hackers associated with Anonymous, Topiary and Sabu, break away from the
collective, recruiting Tflow, Kayla, Pwnsauce and Anonymous supporter avunit to
form Lulz Security or LulzSec.
May 6, 2011: X-Factor
LulzSec
leaks the personal information of the contestants on the UK television show “The
X-Factor”.
May 15, 2011: U.K. ATMs Hack
LulzSec
releases the locations, ID numbers, and owner information of thousands of ATMs
in England.
June 5, 2011: Government email addresses leaked in Middle East
In
support of protesters in the Middle East, Anonymous dumps hundreds of email
addresses and passwords that belong to government officials in Bahrain, Egypt,
Morocco, and Jordan.
June 7, 2011: Sabu arrested
Unemployed
28-year-old Hector Monsegur and alleged LulzSec leader “Sabu” is arrested in
the Jacob Riis housing complex in New York. Monsegur agrees to become an
informant for the FBI while continuing to lead LulzSec.
June 13, 2011: Senate website hit
LulzSec
hacks Senate.gov and the pilfers data online. “We don’t like the US government
very much,” their Twitter feed says. “Their sites aren’t very secure.”
June 15, 2011: LulzSec takes down CIA.gov
LulzSec
launches DDoS attacks on the CIA’s website.
June 16, 2011: Random email dump
LulzSec
leaks 62,000 email address and password combinations for no apparent reason. It
also doesn’t say where they got the information, or how. In a tweet, LulzSec
urges its followers to use the information to break into Facebook, Twitter,
World of Warcraft, and other sites.
June 20, 2011: LulzSec turns to the UK
AntiSec
shuts down the website of The Serious Organised Crime Agency, an elite law
enforcement unit in the U.K., marking the first time LulzSec has gone after a
British law enforcement agency.
June 21, 2011: Alleged LulzSec member arrest
Scotland
Yard arrests 19-year-old Ryan Cleary, an alleged member of LulzSec, in Essex,
England. LulzSec denies Cleary’s involvement.
June 25, 2011: LulzSec calls it quits
LulzSec
announces the end of their famed 50-day run, releasing a statement saying that
they have accomplished their mission to disrupt corporate and government
bodies. “Our planned 50 day cruise has expired, and we must now sail into the
distance, leaving behind - we hope - inspiration, fear, denial, happiness,
approval, disapproval, mockery, embarrassment, thoughtfulness, jealousy, hate,
even love,” the statement says.
July 11, 2011: Military email addresses released
Military
consulting firm Booz Allen Hamilton is hit with a data breach that leads to a
data dump of 90,000 email addresses belonging to military personnel. AntiSec,
another Anonymous offshoot, claims responsibility.
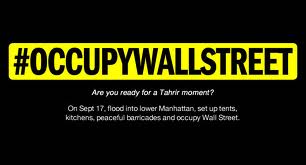
July 13, 2011: Adbusters original Occupy call to action
Sighting
the success of Tahrir (the Arab Spring), #occupywallstreet
reaches out to “90,000 redeemers, rebels and radicals”. “On September 17, we
want to see 20,000 people flood into lower Manhattan, set up tents, kitchens,
peaceful barricades and occupy Wall Street for a few months. Once there, we
shall incessantly repeat one simple demand in a plurality of voices.”
July 19,
2011: PayPal 14 arrests
The FBI arrests the so-called “PayPal 14,” reputed Anonymous
members that allegedly launched a DDoS attack against PayPal, after the online
payment servicing company, along with Visa and MasterCard, stopped processing
donations for WikiLeaks. In this clip from We Are Legion: The Story of the
Hacktivists, Attorney Stanley Cohen talks about DDoS as a means of protest.
July 19,
2011: “Anonymous 16” Arrested
The U.S. Department of justice announces that sixteen people
allegedly associated with Anonymous were arrested for PayPal DDoS and other
attacks.
July 27,
2011: Alleged LulzSec member ‘Topiary’ arrested
British police in the Shetland Islands arrest Jake Davis, an
18-year-old hacker and alleged LulzSec member Topiary.
August 23,
2011: Anon aligns with Occupy
Anonymous releases a video in support of Occupy Wall Street and
joins the September 17th occupation organized by Adbusters Magazine.
September
17, 2011: Occupy Wall Street Begins
Occupy Wall Street begins in Zucotti Park in New York City’s Wall
Street Financial district
February
3, 2012: Scotland Yard-FBI phone call intercepted and released
Anonymous posts a 16-minute recording of a phone call between the
FBI, Scotland Yard and other foreign law enforcement agencies discussing their
investigation into the hacktivist collective.
February 3,
2012: Occupy Boston Police Department takedown
In response to Boston police’s treatment of Occupy protesters,
Anonymous takes down the website of the Boston Police Department.
February
5, 2012: Syrian anons dump government emails on Wikileaks
A Syrian offshoot of Anonymous hacks into numerous servers and web
domains in the country, stealing over 2 million email addresses that belong to
government officials and contractors. The data is then given to WikiLeaks,
which publishes it in July.
February
29, 2012: Interpol site down
Anonymous brings down the Interpol’s website, after the law
enforcement agency announces the arrests of 25 suspected Anonymous members.
March 6,
2012: Sabu Outed as FBI Informant
News breaks that Hector “Sabu” Monsegur,
the alleged leader of LulzSec, has been acting as an informant for the Federal
Bureau of Investigation.
March 7,
2012: Vatican hack
Anonymous’ Italian faction takes down Vatican’s website with a
DDoS attack, in protest of the church’s handling of the sex abuse scandals, its
teachings on birth control, as well as its burnings of heretics during the
Inquisitions.
March 30,
2012: @AnonymousChina
In a week-long spree, Anonymous’ China branch shuts down and
defaces close to 500 government, company, and other miscellaneous websites.
Email addresses and phone numbers of Chinese government officials are also
leaked.
April 7,
2012: Anons attack .gov.uk sites
Anonymous shuts down multiple UK government websites with DDoS
attacks, in opposition to the country’s proposal to monitor all web and phone
traffic.
May 9,
2012: Putin protests
Anonymous disables websites of Russian President Vladimir Putin
and the Kremlin, in support of the massive street protests in the country
against Putin’s third term as president.
June 14,
2012:Oil companies email attack
In Operation Save the Artic, Anonymous steals email information
from the websites of Shell, Exxon, BP, and Russian oil firms Gazprom and
Rosneft to protest oil drilling in the Arctic.
To keep up with these developments and more, please check back
with the Timeline at the We Are Legion Documentary website.
This is the second entry in a series about Hacktivism:
- Part One, The uprising
- Part Two, We are Legion: the History of Hacktivism
- Part Three, The Future of Hacktivism: the Collective Party
- Part Four, Cyberwars: a far bigger threat than hacktivists
- Part Five, So how should a bank protect itself from hacktivists and cybercrime?
Chris M Skinner
Chris Skinner is best known as an independent commentator on the financial markets through his blog, TheFinanser.com, as author of the bestselling book Digital Bank, and Chair of the European networking forum the Financial Services Club. He has been voted one of the most influential people in banking by The Financial Brand (as well as one of the best blogs), a FinTech Titan (Next Bank), one of the Fintech Leaders you need to follow (City AM, Deluxe and Jax Finance), as well as one of the Top 40 most influential people in financial technology by the Wall Street Journal's Financial News. To learn more click here...