We’ve seen some pretty strong attacks on banks cyberdefences in the past year. Three major incidents in the SWIFT network; 50 at the Federal Reserve; problems at the Bank of England and many other central banks; a major incident at the Danish payment processorNETS; and big banks like HSBC and JPMorgan have all been affected.
Admittedly, most of these are DDoS – Distributed Denial of Service – attacks, which bring down websites but not banks, yet that’s just the tip of the iceberg. After all, it used to be that thieves would rob bank branches as that’s where the money was; now, they rob bank servers because that’s where the money is.
These incidents of cybercrime are often unnoticed however, as banks are loathe to go publish and say they were hacked … but one did just that this week. Tesco Bank. A hacker got into the bank and compromised 40,000 of their 136,000 accounts. That’s a third. Of those compromised, the bank originally thought that 20,000 had been hacked with money taken, bvut it turns out it is 9,000 who lost £2.5 million ($3.2 million). Even so, the bank had to shut down their internet banking service to all customers for several days, whilst they sorted out the mess, and suspended all online debit card and contactless card transactions.
That is seriously worrying for a bank’s reputation. They’ve promised to reimburse all customers who were impacted, but to openly say they were hacked is not good for the image.
But hey, Tesco is a small bank. It couldn't happen to a big boy could it? Urmmm … read the opening paragraph. So what’s the solution?
Well cybertheives are really good at sharing what works and doesn’t work. Using the Dark Net and chat rooms, they share huge amounts of information from credit card details to usernames and passwords to offering any delicacy you might dream for. Why don’t banks do the same? Now they do.
From Bloomberg, there’s a really interesting discussion with Troels Oerting, Group Chief Security Officer (CSO) and Group Chief Information Security Officer (CISO) at Barclays:
“The organized crime groups in cyber are sharing much better than we are at the moment,” says Oerting, a Dane with a square jaw and the watchful eyes of a cop who’s investigated the underworld for 35 years. “They are sharing methodologies, knowledge, tools, practices—what works and what doesn’t.”
Now he and his counterparts at other big banks are doing some networking of their own. Oerting, who led the European Cybercrime Centre in The Hague before joining Barclays in 2015, has assigned some of his people to join allies from four other big U.K. banks at an operations center in London’s Canary Wharf complex. They sit side by side with police officers from the U.K. National Cyber Crime Unit.
The idea is that this industry-government “fusion cell,” the Cyber Defense Alliance, will let the sleuths swap tips, techniques, and hunches the same way the bad guys do. “To do this right, you need to have trust,” Oerting says. “If I give information to another bank about my breaches, I don’t want to see this on the front page of the newspaper the next day.”
The effort, the first of its kind in the U.K., mirrors a similar initiative in the U.S. called the National Cyber-Forensics and Training Alliance, a nonprofit in Pittsburgh that brings together academics, corporate security executives, intelligence operatives, and law enforcement officials. Barclays has also installed an analyst at Interpol’s cyber investigations unit in Singapore.
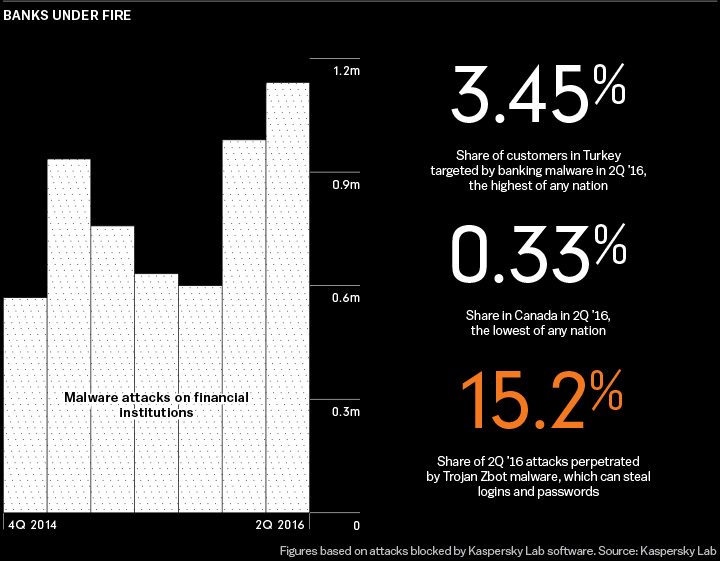
Joining forces marks a big change for institutions long reluctant to share information about their IT systems, let alone how they’re compromised. They’ve decided they better reboot that mindset fast if they want to counter the online onslaught assailing their walls. In the second quarter of this year, cybercriminals tried to inject more than 1 million malware programs into financial companies worldwide, a 50 percent jump from the same period in 2015, according to Kaspersky Lab, a global cybersecurity company …
Maybe Tesco needs to join the Cyber Defense Alliance … oh no, too late.
Chris M Skinner
Chris Skinner is best known as an independent commentator on the financial markets through his blog, TheFinanser.com, as author of the bestselling book Digital Bank, and Chair of the European networking forum the Financial Services Club. He has been voted one of the most influential people in banking by The Financial Brand (as well as one of the best blogs), a FinTech Titan (Next Bank), one of the Fintech Leaders you need to follow (City AM, Deluxe and Jax Finance), as well as one of the Top 40 most influential people in financial technology by the Wall Street Journal's Financial News. To learn more click here...